Most recent News & Articles
OCBC introduces program to aid women entrepreneurs
The programme offers tailored financing solutions, educational workshops, and networking and mentorship opportunities.
Allianz Partners takes top prize for MAvalue app at Qorus Reinvention Awards – Europe 2024
Last month at the Qorus Reinvention Awards – Europe 2024, Allianz Partners won the Operational Efficiency gold award for MAvalue,...
Innovation Masters: Banks at the forefront of women's business empowerment
A selection of innovative projects empowering female entrepreneurship, submitted for the Qorus Banking Innovation Awards in recent years by KCB,...
MetLife Pet Insurance partners with the Association of Animal Welfare Advancement
MetLife Pet Insurance and the Association of Animal Welfare Advancement (AAWA) have joined forces to address pet owners' challenges in...
KBC announces plans for cutting-edge data centers in Belgium
These state-of-the-art facilities are not only set to enhance KBC's ability to deliver top-notch services but also signify a significant...
Lemonade expands homeowners insurance offering in France
Lemonade, the digital insurance company, has expanded its offerings in France by introducing Homeowners insurance in partnership with BNP Paribas...
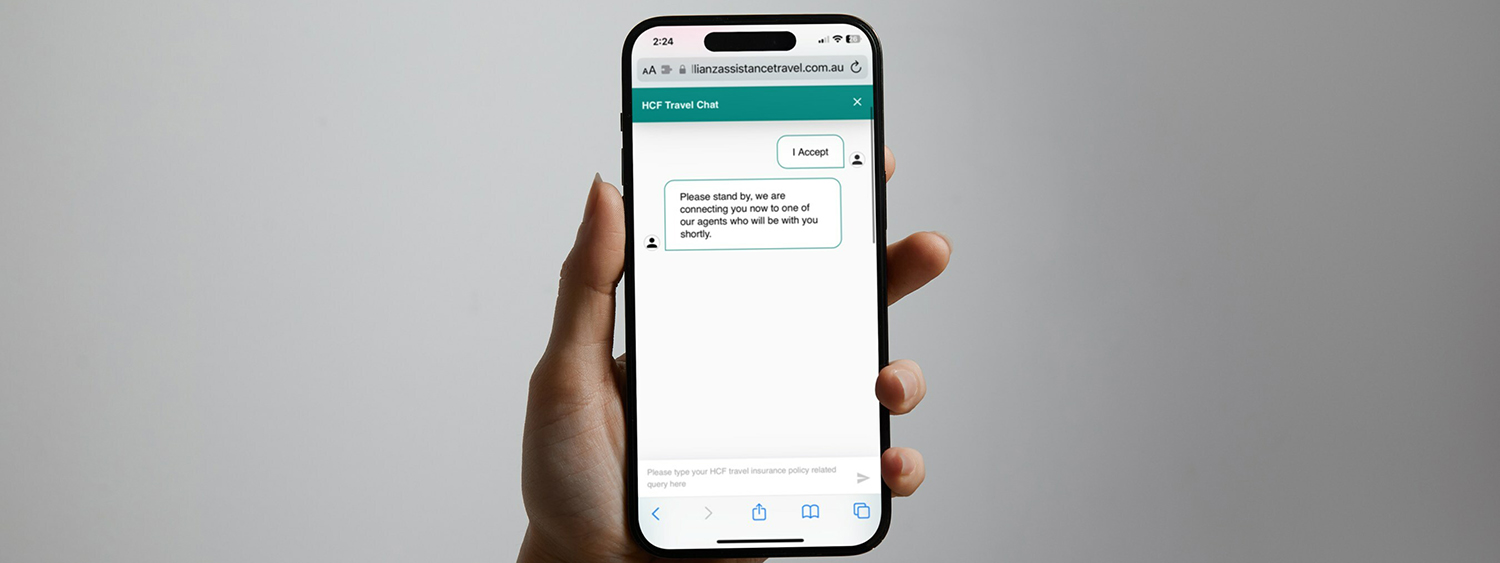
Allianz Partners introduces instant online chat for HCF travel insurance customers
This pioneering service furnishes HCF members with real-time support for their travel queries, broadening the avenues through which customers can...
Most recent Studies & Reports
Driving forces: The interplay of financial services and the EV sector
The financial services sector and the electric vehicle (EV) sector are two dynamic realms undergoing a significant transformation in today's...
A bancassurance breakthrough: Nurturing SME relationships through customized insurance products
In this paper, we outline the opportunity bancassurance presents to banks, as well as the key considerations that should be...
Innovation Radar: Reinvention Awards Europe winners 2024
Discover the most innovative projects from banks and insurance companies in Europe.
Unleashing SME banking potential with embedded finance: Simplifying financial services to create unprecedented convenience for SMEs
In this paper, we will unravel the key challenges that banks need to address to not only navigate the upcoming...
Latest innovations
Video consulto medico specialistico per FASDAC
Traditional medicine has evolved and thanks to telemedicine Generali Welion offers the opportunity to contact medical specialists through a digital...
STARBENE package
As from 1 March 2023, Generali has launched the new "Health&Welfare" organisational unit: a unique model on the Italian market...
Europe’s leading insurance as a service platform
Traditional insurance providers often cling to outdated products and processes and remain stuck in a rut of inflexibility and resistant...
Intelligent Claims Settler (ICS)
This AI-based solution combines customers’ health information, extracted from the medical documents provided, with his/her insurance coverage in order to...
Join the Qorus
Today, Qorus is a catalyst for reinvention for our financial services members by helping them to go further, be faster and work together.
Forthcoming events
Integrating biodiversity and nature risks into climate risks in financial institutions
In today's changing environmental landscape, integrating biodiversity and nature risks into climate risks is pivotal for financial institutions. Understand the interconnected challenges and explore best practices in navigating this complex terrain.
Cybersecurity: The role of the banks and insurance
Examine symbiotic relationships between financial institutions and embedded cybersecurity insurance, emphasizing collaborative efforts against digital risks and cyber threats.
Reinvent Forum Lisbon
Reinvent Forum Lisbon - is dedicated to the digital transformation influencing the insurance sector. Our event brings together industry leaders, experts, and innovators to delve into the latest trends and strategies for enhancing customer satisfaction through innovative digital endeavors. Attendees can expect profound insights into the evolving landscape of insurance.
Electric vehicle charging
Future position of insurance in mobility will be shaped by ongoing technological advancements, changing consumer behavior, and evolving regulatory frameworks. One of the key roles of insurance in mobility will be to provide coverage for new and emerging risks associated with the use of new technologies, such as autonomous vehicles...
Climate change and insurance gap
Climate change intensifies the insurance gap, driving a surge in extreme weather events and economic losses. Join our online event to collaborate on building a more resilient future in the face of climate change.
We help banks and insurers to reinvent themselves to thrive.
 Further
Further
We curate inspiring and innovative projects, technology and ideas so individuals, teams and organisations can collectively create the future of financial services.
 Faster
Faster
We’re a catalyst for reinvention, improving revenue generation, creating efficiencies, redefining customer experiences and forming profitable relationships.
 Together
Together
We're a neutral space where members unite to share, learn and collaborate, thinking freely to solve problems through an ecosystem of unique, specialist communities.












.png)





